Thursday, October 2, 2008
Power Supply
Thursday, September 18, 2008
More information about A.S.I.Eye
 mply call him BOSS (original content of network sniff):
mply call him BOSS (original content of network sniff):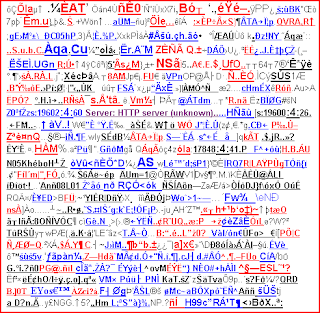 This should prove the existence of all seeing internet eye. Take a closer look this happens to most people everyday when they surf the internet as usual. Most machines will likely be part of a stealth information bot collection system and part of a vicious secret chat community.
This should prove the existence of all seeing internet eye. Take a closer look this happens to most people everyday when they surf the internet as usual. Most machines will likely be part of a stealth information bot collection system and part of a vicious secret chat community.Sunday, August 17, 2008
Core Problem: static http/s tunneling
Ethernet and Router as gates?
It is crucial to create awareness so that many people don´t waste their time trying to hit the evil on the wrong side. Visualize about a Zombie (Exploit, Virus) that always stands up no matter how hard you hit him (security tools) he will always come back. It won´t help if you bash him (regular updates, system hardening, backups) it also won´t help if you start using haphazardly weapons (antivirus, antispy..) you may blast him away a part of his body but he will stand up again and again. You must analyze how it is constituted to get a possibility to punch evil on the right side.
Sunday, August 10, 2008
The ultimate tunnel?

I made some experiments trying to see how the assumed all seeing and all bypassing internet eye would react on restrictions. I started to install top of the notch firewall, using latest updates, 64 bit, windows vista, restriction/block of java, javascript, images, animations, referrers, cookies, ads, frames, surfing to google, in short I blocked quasi all.
Usually one should expect not much traffic at all and repetitive traffic but what happens? We see variable byte traffic can we now conclude a all bypassing tunnel?
Check yourself what do you think?
Thursday, August 7, 2008
Why no full encryption?
This question can´t be answered directly but I can give you hints and impulses for their reasons. One cause could be the paradigm of nature they simply copy the system of nature because they assume that nothing can be more perfect then that what nature has done. They took a look into DNA and RNA and simply thought it could be a good idea to use it as paradigm. The All Seeing Internet Eye wants to be the root of the root and what is the root of the root? The genomic structure especially Deoxyribonucleic Acid the repository of the genetic information. What we see if we take a fast look into it? We see two things coding and decoding, encryption and decryption.
Expressed regions and intervening regions and what is the catalytic effect to create a encryption that is the new buzzword of it security scene: Splicing. Unencrypted information (intron) and encrypted material (exon), catalyzer (splicing). I am no bio scientist I only compared some parts of biology with things that happens when taking a look into net packets and saw a common denominator. Remember the question? Now you have one possible idea. Think about something that wants to dominate everything on this planet it has to go to the deepest root of being and change its structure to fit the needs of this hidden thing. If we would carry on this thought The All Seeing Internet Eye could be invented for only one aim: World Domination or World Control.
Wednesday, August 6, 2008
A short view inside the Eye
@ = Behind this you´ll find mostly the addressee within a covert channel communication but it could be also something like a directed command. Don´t expect the name always displayed immediately behind or before this sign.
EAU, H2O, AQA, AGUA (obfuscated: E/A#U, A°Q~A, A#G*``U+A, ÆÅÛ, ËÄÚ, ÀÊÛ(permutated)) = Reason for this secret word could be the omnipotent power of water that trams its way through all barriers.
SPY = If you find this word you will be alerted, I think there is no need for further explainations.;-)
NL, UK, RU, JP, CZ, PL, FI, SE, SVE, USA, BR... = Specification of countries probably to assign the regions.
EYE obfuscated variant 1. “( S\ɲ¥Ë variant 2. ®‘Ê*ÿè. variant 3.”È ”.°Ÿ.Ê = The All Seeing Internet Eye? Naturally?!
AV = A.V. = Check if Antivirus is present or not.
FW = Check if Firewall is present or not.
PU obfuscated ‘¤P‰.Ù, P.–®U = I am not sure about its meaning but it is used since the beginning.
AM, FM, UKW = Possible radio frequencies that might be used.
AM, PM (..P›m.) = ante/post meridiem (time for their actions)
ON, OFF = someone who signed on or off and is tracked by the All Seeing Internet Eye.
OS = Operation System
EPO, ËPÔ? = Entrypoint Obscuring.
PI = Several possibilities e.g. Private Investigator, Process Integration, PI, principal inv.
PI:0 or PI0 = PID 0 = possible System Idle Process Walker
OP = Operation (possible commands)
GO = Go, Start (possible commands)
SAY = possible command
AXE = Location axe of the tracked system
ASE aka àŠÉ aka ä.S°.E = All Seeing Eye
? = some times questioning to other users of this hidden system
ACL = Access control list
<> = not present, not available, not there
AES, ÆS = AES encryption algorithm
CU, C-Y, see U = see you (possible chat comments)
OK = Okay (possible chat comments or command)
Vca, Vco = voltage controlled amplifier/oscillator
Cd, Iso, Raw, Rau = probably filesystem or transmission level
bye, by, ByE = Bye (possible chat comments or command)
Jeu = Game, Vx = Virus, Rue
Rñ41, Rn41 = Bluetooth DIP Module, Metall Resistors, Vpn, VoIP
VM, VM5 = possible parts of their virtual machine network
PW = Password lookup
Z = Zombies, Z0-14 e.g. probably their way to assign Zombie PCs.
Hel = HE¦L*.!¡„.. = original meaning of: to hide something
BB = B.B = BigBrother: ultimate symbol for espionage
BOT = BÔT = BOTHZ = naturally? Keyword for mass remote control of computers.
FOE = F0Ë. = FO = naturally?!
HQ = H.Q. = Headquarter of their experiments.
WÒ = WO = Where
I post this point of view in the hope it will help others to partially decipher a potential or possible underestimated global and pandemic internet threat. Soon, more news.
Port 80
Surf a simple page that does not change its content several times and always catch the traffic you may notice that the substance is not always the same despite the fact that you did everything like before. How is that possible?
One explaination could be the All Seeing Internet Eye. Something that stands in the middle between you and your destination something that tracks everything you do and contemporaneous seems to operate as autonomous system controlled either artificially or by human being.
Introduction
Nowadays we have more threats to face then ever when surfing the internet, the more experienced we become the more scepticism may occur. No day goes by without horror news about sophisticated malware and the permanent progression of pests. "Human being the most cunning of all animals" once was said. In Internet this phrase reaches a new quality. The importance of the web grows day by day and more and more people become dependent on it.
But the most hidden thing could be located in your net packets. Be aware that I make a subjective statement there is no guarantee for my assertions.
I know that many people have a vague impression about something that is deeply hidden in their systems. They try to protect themselves with antiviruses, firewalls, antispys, antirootkits or security suites, keep their systems examplary up-to-date but they still feel surveilled and this for good reasons.
Many security forums are not well-disposed if people post things about unknown occurences and possible conspiracy theories about global danger and spy attacks, multiplatform malware from the hidden. In many cases the established forum mob intends to shift all those people into paranoid area and try to kick them out of focus. Unfortunately many voices become silent due to the pressure and attacks they receive for their discoveries. There must be a reason why so many try to run dry the revelations of unknown and hidden things and no the reasons are not because all those claims are invented but because we hit the nerve of something that wanted to stay hidden and now yells out. Events like this are real more real then most might believe. I will try to give a little impression of what I observed.